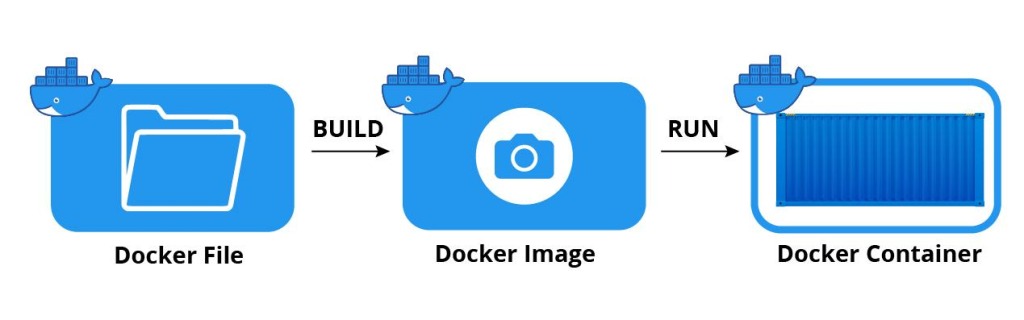
You’ve probably heard of Docker by now. It’s an open-source platform that allows you to develop, deploy, and run applications by using containers. In a nutshell, containers will enable you to package up an application with all the dependencies it needs to run on any machine with a Docker Engine installed.
Docker has become incredibly popular in recent years because it makes it easy to create portable, scalable applications. However, Docker images can be vulnerable to attack if they’re not adequately secured. That’s why it’s essential to know how to secure your Docker images. For example, with the kubernetes registry, you can use image scanning tools to detect vulnerabilities in your images and ensure that only trusted images are used in your deployments, according to jFrog. Additionally, you can set up authentication and authorization for your Docker registry to control who has access to your images.
- Use Official Images whenever possible: The Docker team maintains a library of official images for popular software applications. These images are vetted for security vulnerabilities and malware before they’re made available, so using them is one of the best ways to ensure that your images are secure.
- Don’t Use Latest Tag: The “latest” tag on an image is subject to change at any time. That means that if you use the latest tag, you could be running an outdated or vulnerable version of an image without even knowing it. It’s much better to specify a specific version or tag when pulling an image from a repository to ensure you’re always running the most recent and secure version.
- Create Minimal Images: One of the benefits of using containers is that they’re very lightweight and efficient. You can further increase efficiency by creating minimal images that only include the bare necessities required to run your application. By slimming down your images, you also make them more difficult for attackers to exploit since they will have fewer components to target.
- Add a Unique Tag for Each Image Version: When you update your images, it’s important to add a new and unique tag toidentify which version is which easily. This will come in handy if you ever need to roll back to a previous version for any reason, like if there’s a security breach!
- Scan Your Images for Vulnerabilities Regularly: Once your images are built and tagged, you should scan them regularly for vulnerabilities using a tool like QualysContainerScanningor Clair from CoreOS. These tools will help you identify any security issues so that you can patch them quickly before attackers can exploit them.
Store Your Images In A Private Repository
By storing your images in a private repository, you’re limiting access to only those with the proper credentials. It’s also important to regularly update the credentials for your repositories to ensure continued security. This can prevent unauthorized users from accessing or tampering with your images.
You can begin storing it with a private repository such as Docker Trusted Registry or a cloud provider like AWS or Google.
Harden Your Security Settings
Docker allows you to set various security options in its configuration file, such as user namespace remapping and image signing. Take some time to review these settings and ensure that they’re correctly configured for your individual needs. You can also use a tool like Docker Bench for Security to check and monitor the security of your Docker setup.
Keep in mind that securing your images is just one aspect of overall cybersecurity – don’t forget about other essential measures like regularly updating software, using strong passwords, and monitoring network activity. Stay safe out
Limit Elevated Privileges Within The Container
It’s generally a good practice to run your containers with the least amount of privileges required for them to function properly. This means avoiding running your containers as the root user and instead using a non-privileged user within the container. You can also use Docker security options like “drop-cap” to restrict the capabilities available in a container and limit potential damage if it were to be compromised.
By putting these measures in place, you can reduce the risk of attackers gaining elevated privileges within your containers and causing harm to your system.
Also, remember to regularly update any software within your containers to ensure they have the latest security patches and fixes.
Use Labels And Annotations To Track Image Changes
You can track the changes made to your images over time by using labels and annotations. This can help identify potential security issues and quickly roll back to a previous version if necessary.
It’s also important to regularly review these changes and ensure that only authorized users can modify your images.
Last Updated: November 23, 2022